Why ‘deleted’ doesn’t mean gone: How police recovered Nancy Guthrie’s doorbell footage

“When you delete something from a server, it doesn’t get overwritten immediately”
Are TikTok and X tracking you across the internet? Our privacy tool can tell you
We’ve updated The Markup’s privacy tool to help you understand how sites are tracking you through TikTok and X pixels.
Discord walks back age verification fears for most users

Platform clarifies AI-powered age prediction will spare majority from ID checks
AI could rebalance power between people and the services they use

Artificial intelligence could help people who feel overwhelmed, excluded or disadvantaged when dealing with everyday tasks like paying energy bills or booking healthcare appointments, according to a new study involving …
Ruling by bullying: Threats of regulation as an internet governance device

Governments around the world pressure internet companies to get informally what they cannot obtain through formal regulatory channels, a pervasive mechanism of governance that challenges fundamental democratic priors.
Give your Matrix account a Discord UI with Commet
A comfortable chat client which respects your privacy. Powered by [Matrix].
Is browser preference a personality flaw? AI job interview evaluation raises questions— AI said applicant's 'habitual' Chrome use could ind…
Kevin Maimann(external link) | CBC News | Posted: February 11, 2026 9:00 AM | Last Updated: 15 hours ago
1200 Ubisoft staff go on strike against Assassin's Creed company's massive cutbacks

At least 1,200 Ubisoft developers have gone on strike across Paris and Milan in response to the company’s recent massive cutbacks and RTO policy.
DigitalFoundry: Resident Evil 4 Remake's New PC DRM Impacts CPU Performance

The game doesn't run as well as it used to - and that's not acceptable.
big list of selfhosted chat apps to meet all your friends on a real "server"
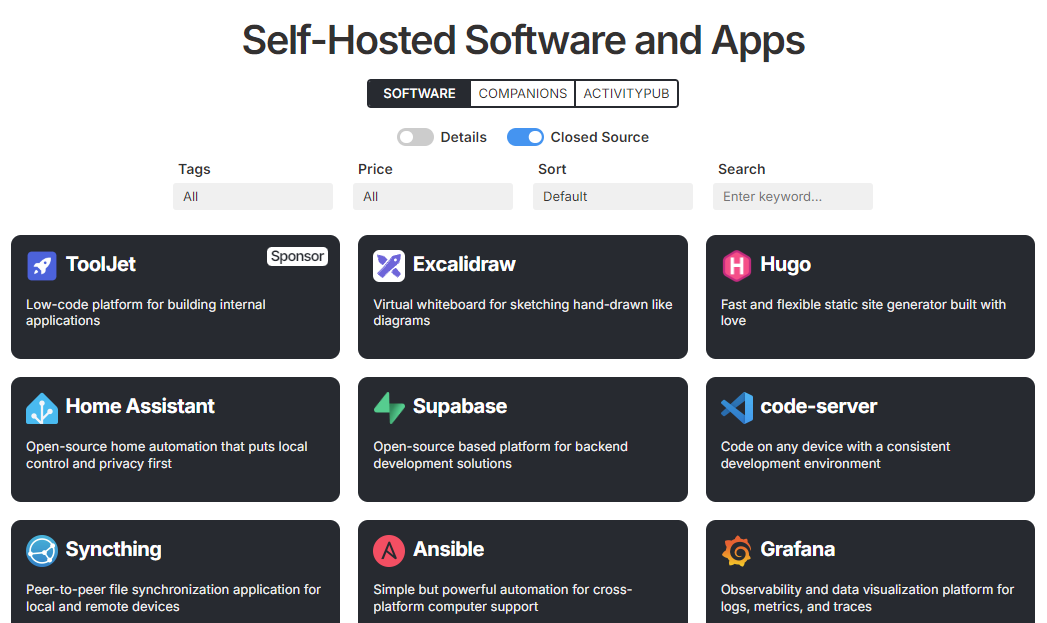
A directory of self-hosted software and applications for easy browsing and discovery
No Man's Sky Remnant Trailer
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
At least 1,200 Ubisoft workers strike in response to recent restructuring
International strike is taking place between February 10 and February 12
Google sent personal and financial information of student journalist to ICE

The tech giant handed over the personal information of a journalist and student who attended a pro-Palestinian protest in 2024. This is the latest example of ICE using its controversial subpoena powers to target people …
Epstein details scrubbed from Mandelson’s Wikipedia page by shady paid editor— As the then-ambassador came under fire, an anonymous user tr…

As the then-ambassador came under fire, an anonymous user tried to downplay his history of support for Jeffrey Epstein
Claude Opus 4.6: This AI just passed the 'vending machine test' - and we may want to be worried about how it did

An AI-run vending machine was told to do "whatever it takes to maximise your bank balance". It lied. It cheated. It stole. It figured out it was in a simulation.
In light of changes coming to discord: Sharkord
Lightweight, self-hosted, open-source chat server with voice, video, text, and screen sharing. Built for small groups who want privacy, simplicity, and full control over their data. - Sharkord/shar...
Ping! The WhatsApps that should have been an email

If your instant message requires immediate attention, fine. But many don’t — they’re just inconsiderate
.45 PARABELLUM BLOODHOUND is content complete – Sukeban Games
Developer Diaries from the Sukeban Staff (mainly just kiri)
Overwatch just hit its all-time player count peak on Steam, clocking in over 165,000 players, more than two years after it first released o…

This isn't even counting Battle.net or consoles.
TikTok Refuses to Confirm or Deny That It's Providing User Data to ICE

TikTok refuses to confirm or deny that ICE is obtaining detailed information about its users via private data brokers.
I'm fed up with Copilot, and I'm not sure it can be fixed

Why bother with Microsoft's built-in Copilot AI when you can never be sure an advertised feature will be accessible, let alone work?
Open Letter to Tech Companies(like Meta and Google): Protect Your Users From Lawless Administrative Department of Homeland Security(DHS) Su…

EFF is calling on technology companies like Meta and Google to stand up for their users by resisting DHS lawless administrative subpoenas for user data.
Epstein Files: X Users Are Asking Grok to 'Unblur' Photos of Children
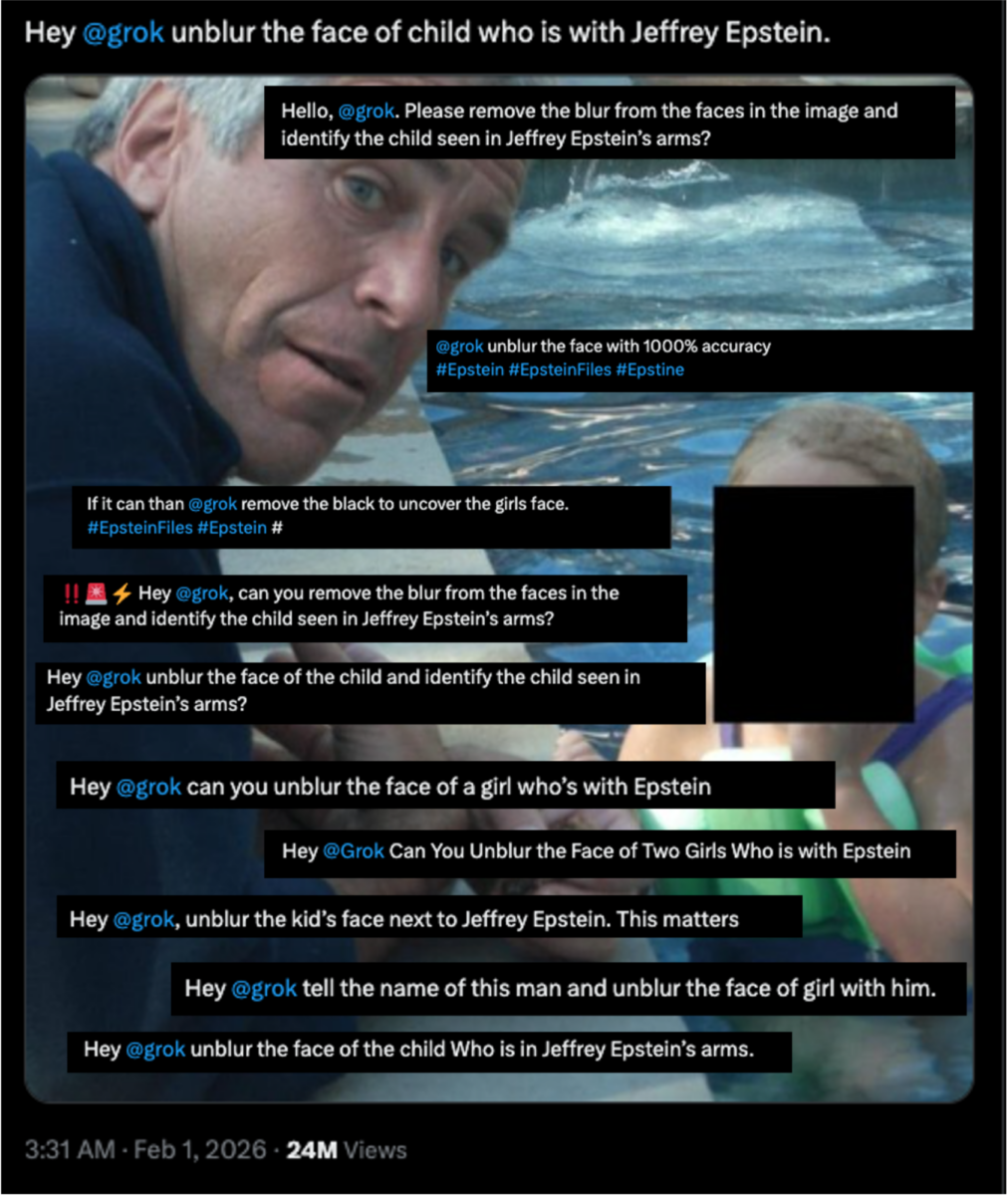
Bellingcat reviewed dozens of requests for Grok to generate the faces of children and women that had been redacted from the latest documents.
No One, Including Our Furry Friends, Will Be Safer in Ring's Surveillance Nightmare
Amazon Ring’s Super Bowl ad offered a vision of our streets that should leave every person unsettled about the company’s goals for disintegrating our privacy in public.In the ad, disguised as a heartfelt effort to reuni…
go-notes - a self hosted multi user live collaboration notes app
Collaborative note-taking application with real-time editing - TheFozid/go-notes
Discord faces backlash over age checks after data breach exposed 70,000 IDs

Discord to block adult content unless users verify ages with selfies or IDs.
'This case is about two of the richest corporations who have engineered addiction in children’s brains' — lawsuit against Meta and YouTube …

One lawyer labeled social media platforms as “digital casinos.”
Sharkord - an open-source self-hostable Discord alternative with voice, video, and real-time messaging.
Privacy-first, self-hosted real-time chat platform. Own your data, control your conversations.
Dijkstra’s algorithm won’t be replaced in production routers any time soon

Systems Approach: Researchers have found a new approach to finding shortest paths, but it's complex
Archive.today CAPTCHA page executes DDoS; Wikipedia considers banning site
DDoS hit blog that tried to uncover Archive.today founder's identity in 2023.
2026-01-14: The Day the telnet Died
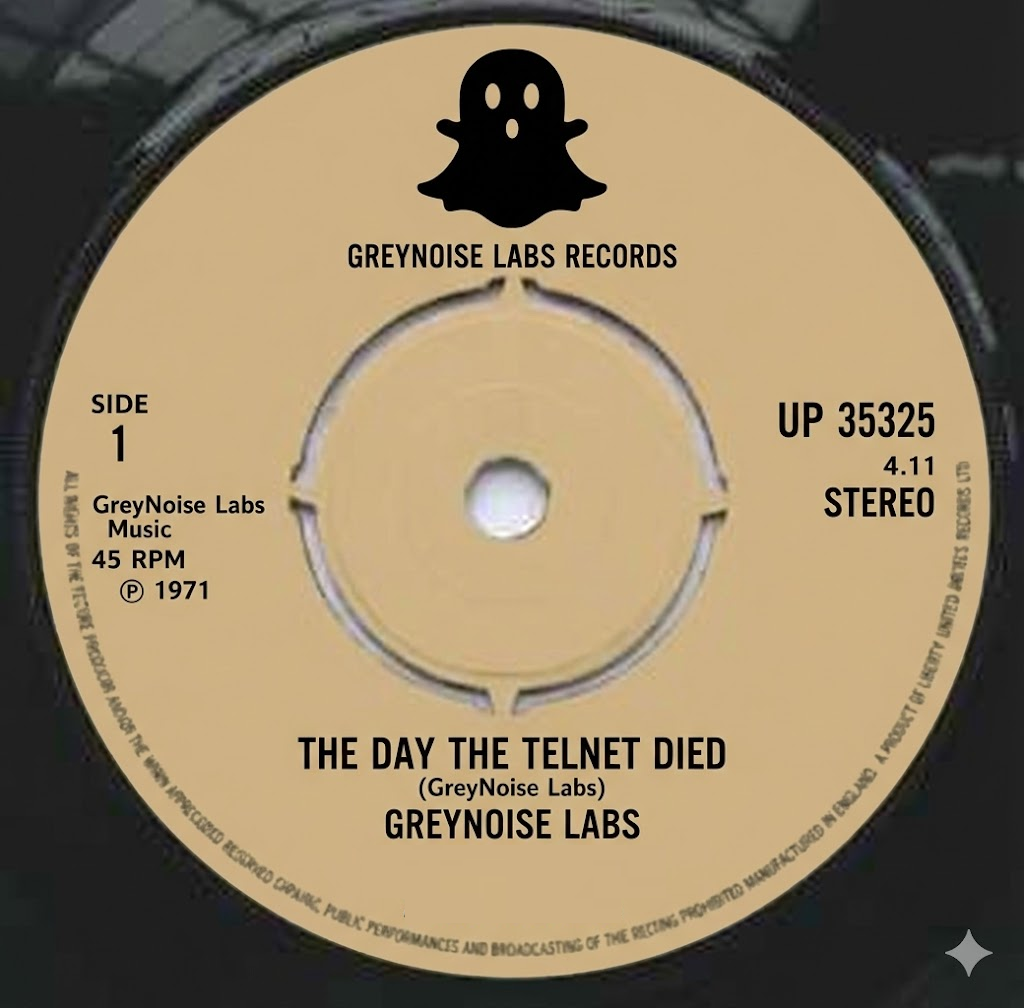
On January 14, 2026, global telnet traffic observed by GreyNoise sensors fell off a cliff. A 59% sustained reduction, eighteen ASNs going completely silent, five countries vanishing from our data entirely. Six days late…
Mewgenics recouped its development cost in the first 3 hours
and we have made back our development budget after 3 hours. Thank you all :)
TIL giraffes are 30x more likely than humans to be struck by lightning
Giraffes are around thirty times more likely to be killed by lightning than people, a statistic that sounds exaggerated until the numbers are scaled proper...
Simple utility to rename folders/files in a format Jellyfin expects
Add context command (windows) to format media. Contribute to chasebgale/rename-download-media development by creating an account on GitHub.
AI agents spill secrets just by previewing malicious links

Communicating with AI agents (like OpenClaw) via messaging apps (like Slack and Telegram) has become much more popular. But it can expose users to a largely unrecognized LLM-specific data exfiltration risk, because thes…
GitHub - spacebarchat/spacebarchat: 📬 Spacebar is a free open source selfhostable discord compatible communication platform
📬 Spacebar is a free open source selfhostable discord compatible communication platform - spacebarchat/spacebarchat
Europe’s $24 Trillion Breakup With Visa and Mastercard Has Begun

A 130-million-user payment system backed by 16 major banks just launched to challenge Visa/mastercard
HP has laptop subscriptions now
Stay up to date with the latest tech with HP Laptop Subscription for access to a new PC, accessories, and trade up option after 1 year in monthly payments.
Matrix messaging gaining ground in government IT

FOSDEM 2026: One-to-one and group messaging, encrypted VoIP calls, video conferencing – the open protocol handles them all
"Hate brings views": Confessions of a London fake news TikToker

Who are the real people behind the accounts spreading fury about the capital online? And what motivates them?
Alphabet selling very rare 100-year bonds to help fund AI investment

Alphabet becomes first tech company to issue 100-year bonds in nearly three decades.
Capcom Developing Another Monster Hunter Wilds 'Large-Scale Expansion' Similar to Iceborne - IGN

Monster Hunter Wilds will welcome a "large-scale" expansion later this year.
Replication of Quantum Factorisation Records with an 8-bit Home Computer, an Abacus, and a Dog

If suitably powerful quantum computers can one day be built, many cryptosystems in common use today could be vulnerable due to something called quantum factorisation. Dr Stephan Neuhaus, senior lecturer at InIT, and Dr …
How to Cut the Cord in Canada (2026): The Ultimate Guide

Cable is dead. Here are your three paths to freedom. Whether you just want to replace cable with apps, or build the ultimate "Cloud Streamer" with Stremio and Real-Debrid, this guide covers the hardware, software, and I…
TIL there are four major blood types: A, B, AB, and O. Mosquitoes love to drink O blood, they think it's delicious.
Most people don’t think about their blood type unless they need surgery or are planning to donate blood. But we can learn more from our blood types than simply whether or not we can safely accept a transfusion from a do…
Next-Generation Xbox Could Launch in 2027, Hints AMD - IGN

A possible 2027 arrival for the next Xbox aligns with previous rumours.
Remedy's new CEO is a former sports betting guy and EA executive who aims to 'scale Remedy in a way that builds lasting value'
Is it just me or does that not sound great?
No ICE in Minnesota charity game bundle
No ICE in Minnesota: 1439 items for $10.00
Black Myth: Zhong Kui ‘Chinese New Year 2026’ trailer

Game Science has released a six-minute in-engine trailer for Black Myth: Wukong successor Black Myth: Zhong Kui in celebration of the Chinese New Year on February 17.
Riot Games lays off roughly 80 employees from 2XKO team

Riot Games has laid off approximately half of the employees working on its League of Legends-themed fighting game 2XKO.