How Hackers Are Fighting Back Against ICE
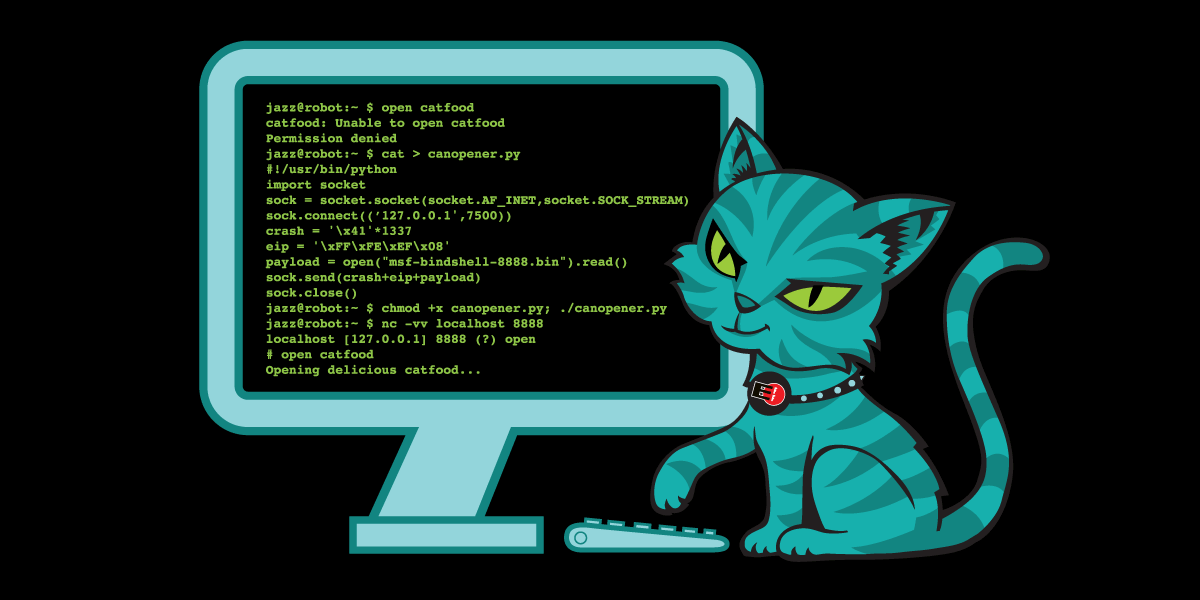
A few enterprising hackers have started projects to do counter surveillance against ICE, and hopefully protect their communities through clever use of technology.
RISC-V Hits 25% Market Penetration as Qualcomm and Meta Lead the Shift to Open-Source Silicon
RISC-V Hits 25% Market Penetration as Qualcomm and Meta Lead the Shift to Open-Source Silicon
TIL why María Corina Machado is relevant in the whole Venezuela thing

María Corina Machado wins the 2025 Nobel Peace Prize for democracy in Venezuela despite her ties to the 2002 coup and support for U.S. sanctions. The Nobel Committee picked someone who supports war crimes over those who…
Meta has discontinued its metaverse for work, too

One more piece of bad news for VR.
We’re All So F’d | NVIDIA x Palantir, Global Surveillance, "Pre-Crime" Arrests, & AI [GNCA - GamersNexus Consumer]
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
AI’s Memorization Crisis | Large language models don’t “learn”—they copy. And that could change everything for the tech industry.

Large language models don’t “learn”—they copy. And that could change everything for the tech industry.
Deliberate Internet Shutdowns - Schneier on Security
For two days in September, Afghanistan had no internet. No satellite failed; no cable was cut. This was a deliberate outage, mandated by the Taliban government. It followed a more localized shutdown two weeks prior, rep…
Tim Cook and Sundar Pichai are cowards - X’s deepfake porn feature clearly violates app store guidelines. Why won’t Apple and Google pull i…

Once you’ve traded your principles for proximity to power, do you even run your own company?
How TF2 Still Makes Millions (With No Updates)
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
Inside the PSL Scale: The Looksmaxxer Rating System That All the Teenagers Are Referencing Are you a mid high-tier normie or subhuman?
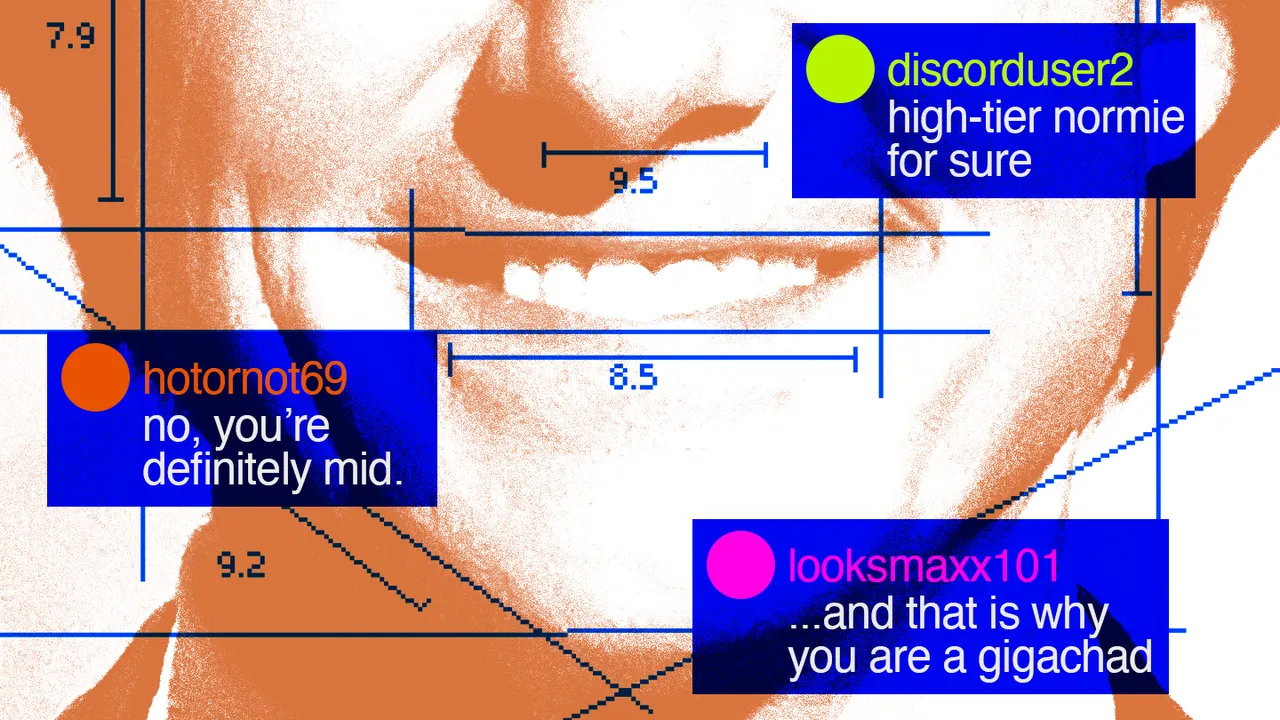
Are you a mid high-tier normie or subhuman? Explaining the guide to attractiveness that’s blowing up on TikTok.
Wikipedia’s Baltic Battle: Estonian Journalists Warn of Coordinated Pro-Soviet Edits, Lithuania Reports Similar Targeting

Estonian and Lithuanian media have recently reported coordinated mass Wikipedia edits aimed at normalizing the Soviet occupation of the Baltic states as legitimate statehood.
Musk lawsuit over OpenAI for-profit conversion can go to trial, US judge says

Judge says there is plenty of evidence to suggest OpenAI’s leaders made assurances nonprofit structure would be kept
Micron addresses Crucial exit backlash: 'We are trying to help consumers around the world' — company warns that DRAM drought could last unt…
Micron has responded to criticism over its decision to exit the consumer memory business and warns that shortages may last until 2028.
‘They’ve pickled each others’ brains’

Longtime entrepreneur and critic Anil Dash speaks with Gazetteer on where the tech industry has been and where it may be going.
Police Unmask Millions of Surveillance Targets Because of Flock Redaction Error
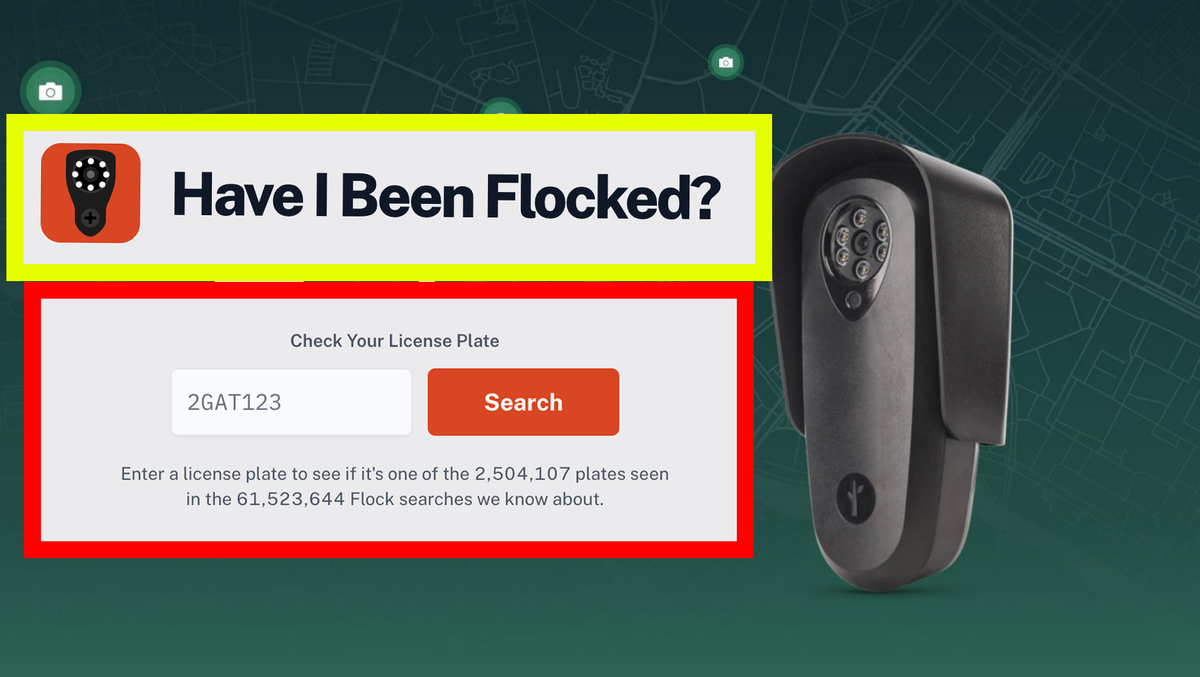
Flock is going after a website called HaveIBeenFlocked.com that has collated public records files released by police.
State of the Fin 2026-01-06 | Jellyfin

Happy New Year and welcome to the State of the Fin!
Over half of enterprise AI stalls on infrastructure mess

: The answer seems to be educating the enterprise workforce, and creating smarter use cases
How Did TVs Get So Cheap? - by Brian Potter

You’ve probably seen this famous graph that breaks out various categories of inflation, showing labor-intensive services getting more expensive during the 21st century and manufactured goods getting less expensive.
X pulls Grok images after UK ban threat over undress tool

: Image generation paywalled on X after ministers and regulators start asking awkward questions
New Social Web Working Group at W3C
Today the W3C standards organization announced a new working group to advance the ActivityPub and Activity Streams standards. The Social Web Foundation, as a W3C member organization, will be partic…
Newer AI Coding Assistants Are Failing in Insidious Ways

One AI coding assistant power user says the tools are hitting a plateau, and some are even declining. What's causing this unexpected twist in tech?
Digital Tribulations 6: A Radical Hacker-Fanonian Critique of Digital Colonialism

The introduction to this series of interviews can be read here. Interview with Deivison FaustinoAt the presentation of the MTST’ book in São Paulo, I met Deivison Faustino, a figure who im
I spent a year on Linux and forgot to miss Windows

One year on Linux, two distros, a few tears, four desktop environments, and zero regrets about leaving Windows.
‘ELITE’: The Palantir App ICE Uses to Find Neighborhoods to Raid

Internal ICE material and testimony from an official obtained by 404 Media provides the clearest link yet between the technological infrastructure Palantir is building for ICE and the agency’s activities on the ground.
'Worst in Show' CES products include AI refrigerators, AI companions and AI doorbells
Artificial intelligence took center stage at this year's CES gadget show, but not always for the right reasons.
Cataloging modern-era physical releases for the Mega Drive and Sega Genesis
Cataloging modern-era physical releases for the Mega Drive and Sega Genesis
TIL encoding and decoding come from Claude Shannon’s work, and "Claude Code" is named after him
The encoding/decoding model of communication emerged in rough and general form in 1948 in Claude E. Shannon's "A Mathematical Theory of Communication," where it was part of a technical schema for designating the technol…
CrowdStrike shareholders lose battle to recoup losses from 2024 outage

: Investors didn't present a valid claim, says judge, but they're welcome to try again
How we get to 1 nanometer chips and beyond

At this year’s IEDM conference, we lay the groundwork for a near future where semiconductors with nodes at 1nm and smaller are possible.
The Making of Disco Elysium - Part One: Foundations
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
Researchers figured out how to run a 120-billion parameter model across four regular desktop PCs

EPFL researchers have developed new software – now spun-off into a start-up - that eliminates the need for data to be sent to third-party cloud services when AI is used to complete a task. This could challenge the busin…
Who and What comprise AI Skepticism?

An attempt to do justice to a diverse community
[Important Update] Postiz v2.12.0 - open source social media scheduling tool
📨 The ultimate social media scheduling tool, with a bunch of AI 🤖 - gitroomhq/postiz-app
The Guardian view on granting legal rights to AI: humans should not give house-room to an ill-advised debate | Editorial

Editorial: Anthropomorphising tech helps Silicon Valley shares to soar, but our empathy should be directed to worthier causes
Is Bambu Lab Next? Washington Eyes Potential U.S. Ban on 3D Printers

Washington reviews Bambu Lab over security risks after DJI. Learn about tariffs, market impact, and Bambu's response in the U.S.
Quitting Spotify for Navidrome

Getting off spotify and rediscovering my own music collection
Google offers bargain: Sell your soul to Gemini, and it'll give you smarter answers

: But private data will stay private and won't be used for training, Google says
AI will compromise your cybersecurity posture
Yes, “AI” will compromise your information security posture. No, not through some mythical self-aware galaxy-brain entity magically cracking your passwords in seconds or “autonomously” exploiting new
Inside ICE’s Tool to Monitor Phones in Entire Neighborhoods

404 Media has obtained material that explains how Tangles and Webloc, two surveillance systems ICE recently purchased, work. Webloc can track phones without a warrant and follow their owners home or to their employer.
Linus Torvalds: "The AI Slop Issue Is *NOT* Going To Be Solved With Documentation"
The Linux kernel developers for months now have been debating proposed guidelines for tool-generated submissions to the Linux kernel
Even Linus Torvalds is trying his hand at vibe coding (but just a little)

But then I cut out the middle man—me."
Danganronpa game simulator
sign up or login to create your own generators ᕕ(ᐛ)ᕗ we only email you at your request (e.g. for password reset) 👍︎
Micron to boost DRAM output with $1.8bn chip fab buy

: Taiwan’s Powerchip sells legacy fab it opened just 19 months ago after spending $9.5 billion
Why the PS5 ROM Leak Could be a Turning Point for Console Security

The PS5 BootROM keys have leaked, exposing unpatchable hardware security and potentially accelerating custom firmware, emulation, and piracy.
Majority of CEOs report zero payoff from AI splurge

: PwC survey finds more than half of 4,500+ biz leaders see no revenue growth nor cost savings
Amazon’s AI ‘Banana Fish’ Dubs Are Hilariously, Inexcusably Bad

Amazon is experimenting with AI dubs on anime and other projects, and what it has done with Banana Fish is downright disgraceful.
Humanoid showdown: Chinese firms make up 55% of robot exhibitors at US tech event

Chinese humanoid robot makers will dominate CES 2026, with nearly a dozen firms and a record Hong Kong delegation showcasing next-gen machines.
Dell admits consumers don’t care about AI PCs, Dell is now shifting it focus this year away from being ‘all about the AI PC.’

Dell is now shifting it focus this year away from being ‘all about the AI PC.’
Building the PERFECT Linux PC with Linus Torvalds
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
Migrating Dillo from GitHub
I would like to migrate the Dillo project away from GitHub into a new home which is more friendly to be used with Dillo and solves some of its problems. This page summarizes the current situation with GitHub and why I d…