Eric Barone makes $125,000 donation to the C# framework Stardew Valley uses, as well as 'an ongoing monthly commitment' in what the team be…

MonoGame has been used to make all sorts of notable games, including Celeste and Bastion.
enclose.horse

A puzzle game about enclosing horses.
Electrolysis can solve one of our biggest contamination problems

ETH Zurich researchers have developed a process that can be used on site to render environmental toxins such as DDT and lindane harmless and convert them into valuable chemicals – a breakthrough for the remediation of c…
Humans May Be Able to Grow New Teeth Within Just 4 Years

Scientists are on the verge of a dental miracle.
Made in space? Start-up brings factory in orbit one step closer to reality

A factory in space has been switched on and has reached temperatures of about 1,000C.
I tested Tech made by Food Brands! by Mrwhosetheboss
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
Hackers threaten to leak massive 'Wired' customer database

The hack affects all Condé Nast entities as well, including the 'New Yorker,' 'Vogue,' and 'Vanity Fair.'
The 10 most anticipated video games of 2026

As 007 makes his gaming return, you can climb a mountain in Cairn, play a scaredy-cat in Resident Evil, and play a criminal couple in GTA VI
Nvidia takes $5 billion stake in Intel under September agreement

Nvidia has purchased Intel shares worth $5 billion, the semiconductor firm said in a filing on Monday, carrying out a transaction announced in September.
(Technology Connections) I made my whole-home humidifier slightly less terrifying [34:38]
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
Findroid v1.0.0 with a complete redesign is here
After more than 1 year, the Compose rework is finally here! ⚠️ This update requires Jellyfin Server 10.11.0+. Please update your server before installing. New features Fresh New Look: Enjoy a com...
Nvidia insists it isn’t Enron, but its AI deals are testing investor faith

The chipmakerâs sprawling partnerships are driving extraordinary growth but also bank its future on the AI boom paying off quickly
Today in “Google Broke Email”
I have just learned that, beginning in 3 days, my employees will no longer be able to receive their work email. Apparently Google is dropping support for Gmail accounts being able to fetch mail from outside accounts. At…
39C3: Liberating ESP32 Bluetooth
Bluetooth is everywhere, but it’s hard to inspect. Most of the magic is done inside a Bluetooth controller chip, accessed only through a controller-specific Host-Controller Interface (HCI) pr…
Librarians Are Tired of Being Accused of Hiding Secret Books That Were Made Up by AI
AI chatbots are generating fake titles that people insist are real.
TIL Russian students are being presented with an ultra-nationalist curriculum, full of militarism and hatred toward Ukraine. 'Mr Nobody Aga…
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
The Rise Of Fake Casio Scientific Calculators

Scientific calculators are an amazing invention that take pocket calculators from being merely basic arithmetic machines to being pocket computers that can handle everything from statistics to alge…
Liz Franczak: Conspiracy and Techno-Capitalism
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
Article: I switched to eSIM in 2025, and I am full of regret
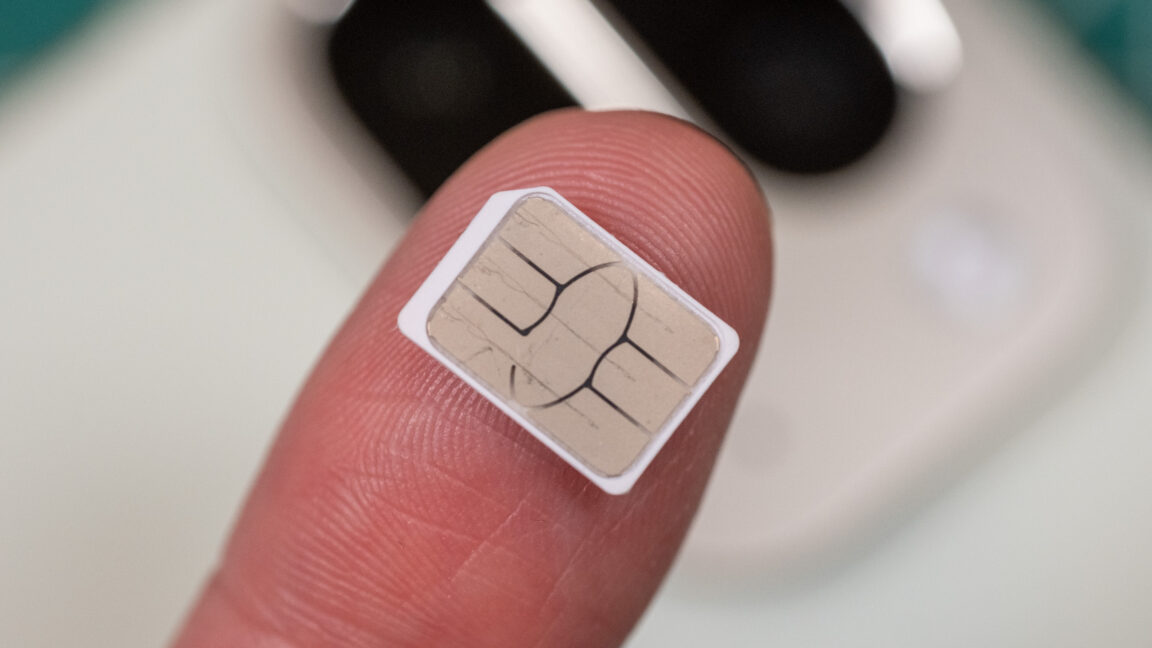
Swapping SIM cards used to be easy, and then came eSIM.
Marvel Rivals - The Super Hero Team-based PVP Shooter

Play for free Now! Get ready to Ignite the Battle with Marvel Rivals!
Ars Technica’s Top 20 video games of 2025

A mix of expected sequels and out-of-nowhere indie gems made 2025 a joy.
The mObywatel's user interface source code has been published

After over one and a half years delay the parts of mObywatel's source code have been published, comprising the user interface of the mobile apps for Android and iOS.
We own the hardware, but not the experience anymore — Big Tech keeps building smarter, more connected devices, but the user experience feel…

Big Tech or Big Brother? We've fallen out of love with Big Tech because our devices feel less like helpful tools and more like strangers in our homes.
The ‘doorman fallacy’: why careless adoption of AI backfires so easily

Human roles are often rich and complex, and not easily reduced to a technological solution.
blog dds: 2025-12-23 — An initial analysis of the discovered Unix V4 tape
Several news outlets reported the discovery of a 1970s Fourth Edition Research Unix magnetic tape at the University of Utah in July 2025 and its successful restoration. This is a significant find, because up to now only…
Salesforce regrets firing 4000 experienced staff and replacing them with AI

Salesforces has entered a phase of public reckoning after senior executives publicly admitted that the company overestimated AI’s readiness
TIL that when Americans migrate from violent states, the risk of future violence follows them

The most violent U.S. regions — Appalachia, the Deep South and the old frontier states — are still deeply marked by a Wild West, stand-your-ground ethos, says a new study co-authored at UC Berkeley.
How Wind Nearly Took Down Boulder NTP

NTP is one of the most interesting and important, but all too forgotten, protocols that makes the internet tick. Accurate clock synchronization is required for everything ranging from cryptography …
Agentic ProbLLMs: Exploiting AI Computer-Use and Coding Agents (39C3)

This talk demonstrates end-to-end prompt injection exploits that compromise agentic systems. Specifically, we will discuss exploits that ...
[Important Update] Postiz v2.12.0 - open source social media scheduling tool
📨 The ultimate social media scheduling tool, with a bunch of AI 🤖 - gitroomhq/postiz-app
A plan for a post-American, enshittification-resistant internet (a speech at 39C3 in Hamburg on Dec 28, 2025)

Trump has staged an unscheduled, midair rapid disassembly of the global system of trade. Ironically, it is this system that prevented all...
Who cares about the Baltic Jammer? – Terrestrial Navigation in the Baltic Sea Region (39C3)

Reports of GNSS interference in the Baltic Sea have become almost routine — airplanes losing GPS, ships drifting off course, and timing s...
Hacking washing machines (39C3)

Almost everyone has a household appliance at home, whether it's a washing machine, dishwasher, or dryer. Despite their ubiquity, little i...
Presenting 14 practical vulnerabilities in GPG & similar tools on stage (39C3)

Might contain zerodays. https://gpg.fail/ From secure communications to software updates: PGP implementations such as *GnuPG* ubiquitous...
Star Citizen is on course to reach $1 billion in player funding in 2026, and we still might not get to play its singleplayer campaign next …

Roberts Space Industries' sim keeps raking in the cash.
All my Deutschlandtickets gone: Fraud at an industrial scale (39C3)

The Deutschlandticket was the flagship transport policy of the last government, rolled out in an impressive timescale for a political pro...
AI content on Wikipedia - found via a simple ISBN checksum calculator (39C3)

I successfully failed with a literature related project and accidentally built a ChatGPT detector. Then I spoke to the people who uploade...
How Hackers Breached the Great Firewall of China (39C3)

The Great Firewall of China (GFW) is one of, if not arguably the most advanced Internet censorship systems in the world. Because repressi...
Expert: EU Commission wants an "unlimited special legal zone" for AI

In a legal analysis for consumer advocates, experts warn of massive protection gaps due to the planned "digital EU omnibus". Big Tech is favored.
What an unprocessed photo looks like
Here’s a photo of a Christmas tree, as my camera’s sensor sees it:
TIL the Sundance Kid lived in Canada for three years

Harry Longabaugh — better known as the Sundance Kid — is perhaps most famous for his daring bank and train robberies as part of Butch Cassidy’s Wild Bunch. But the American outlaw’s short stint as a cowboy and businessm…
'Baldur’s Gate 2: F My Bhaal Femcel Life' - Warlockracy
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
TIL: The word Vatnik is used in Russia and other post-Soviet states for steadfast jingoistic followers of propaganda from the Russian gover…
vatnik - Vatnik (Russian: ватник, pronounced [ˈvatʲnʲɪk]) is a political pejorative used in Russia and other post-Soviet states for steadfa...
MongoBleed explained simply | MongoDB exploit

CVE-2025-14847 allows attackers to read any arbitrary data from the database's heap memory. It affects all MongoDB versions since 2017, here's a simple explanation:
Extremely rare East German game console from the late 1970s tested — only such device produced by communist GDR, bought for $1,000 at aucti…

Machine with just a few Pong variants was snagged for roughly $1,000 in an online auction.
Last Year on My Mac: Look back in disbelief – The Eclectic Light Company

If someone had told me 12 months ago what was going to happen this past year, I wouldn’t have believed them. Skipping swiftly past all the political, economic and social turmoil, I come to th…
The Untold Story of the Nintendo Entertainment System
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.
Petlibro: Your Pet Feeder Is Feeding Data To Anyone Who Asks
How I found critical vulnerabilities in Petlibro smart pet feeders allowing complete account takeover via broken OAuth, access to anyone's pet data, device hijacking, and private audio recordings - and how they're still…
Raspberry Pi Gets Desktop Form Factor

Before the Raspberry Pi came out, one cheap and easy way to get GPIO on a computer with a real operating system was to manipulate the pins on an old parallel port, then most commonly used for print…
Why Are Cars Getting Rid Of Android Auto?

In-car, smartphone infotainment systems are a pro for car shoppers, but not necessarily carmakers who'd rather keep your data all for themselves.